James Carter
Sprint Tokenization: Enhancing Security and Efficiency in Data Protection

In today’s digital landscape, protecting sensitive data has become a paramount concern for organizations across industries. One approach that has gained significant traction is tokenization. Sprint tokenization, a cutting-edge advancement in this field, offers enhanced security and efficiency in data protection. This article delves deep into the concept of sprint tokenization, its benefits, implementation considerations, key features, use cases, challenges, and more.
I. What is Tokenization?
Before diving into sprint tokenization, it’s important to understand the fundamentals of tokenization itself. Tokenization is a process where sensitive data, such as credit card numbers or personally identifiable information (PII), is replaced with unique tokens. These tokens retain no intrinsic value and are used as surrogates for the original data.
II. Introducing Sprint Tokenization
A. Definition of Sprint Tokenization
Sprint tokenization is an advanced form of tokenization that focuses on optimizing security and efficiency. It involves the rapid generation and validation of tokens, enabling swift transaction processing while maintaining data privacy.
B. Benefits of Sprint Tokenization
1.Increased Security
tokenization provides a robust layer of security against data breaches. By replacing sensitive data with tokens, the risk of exposing confidential information is significantly reduced. Even if a breach occurs, the stolen tokens hold no inherent value, rendering them useless to malicious actors. Sprint tokenization enhances confidentiality and privacy by ensuring that sensitive data is not accessible in its original form, even within the organization.
2. Improved Transaction Speed
The agility of sprint tokenization is one of its key advantages. By streamlining the token generation and validation processes, organizations can experience faster transaction speeds. This is particularly beneficial in high-volume environments such as e-commerce or payment processing, where swift processing is crucial.
Sprint tokenization reduces the time required for token generation, enabling seamless and efficient transactions. This improved speed enhances customer experience and supports business growth.
3. Simplified Compliance
Compliance with regulatory requirements, such as the Payment Card Industry Data Security Standard (PCI DSS) or the General Data Protection Regulation (GDPR), can be complex. Sprint tokenization simplifies compliance efforts by aligning with these standards.
By adopting sprint tokenization, organizations can meet data protection standards and ensure the secure handling of sensitive information. It minimizes the scope of compliance audits, reduces associated costs, and mitigates potential risks.
III. Implementing Sprint Tokenization
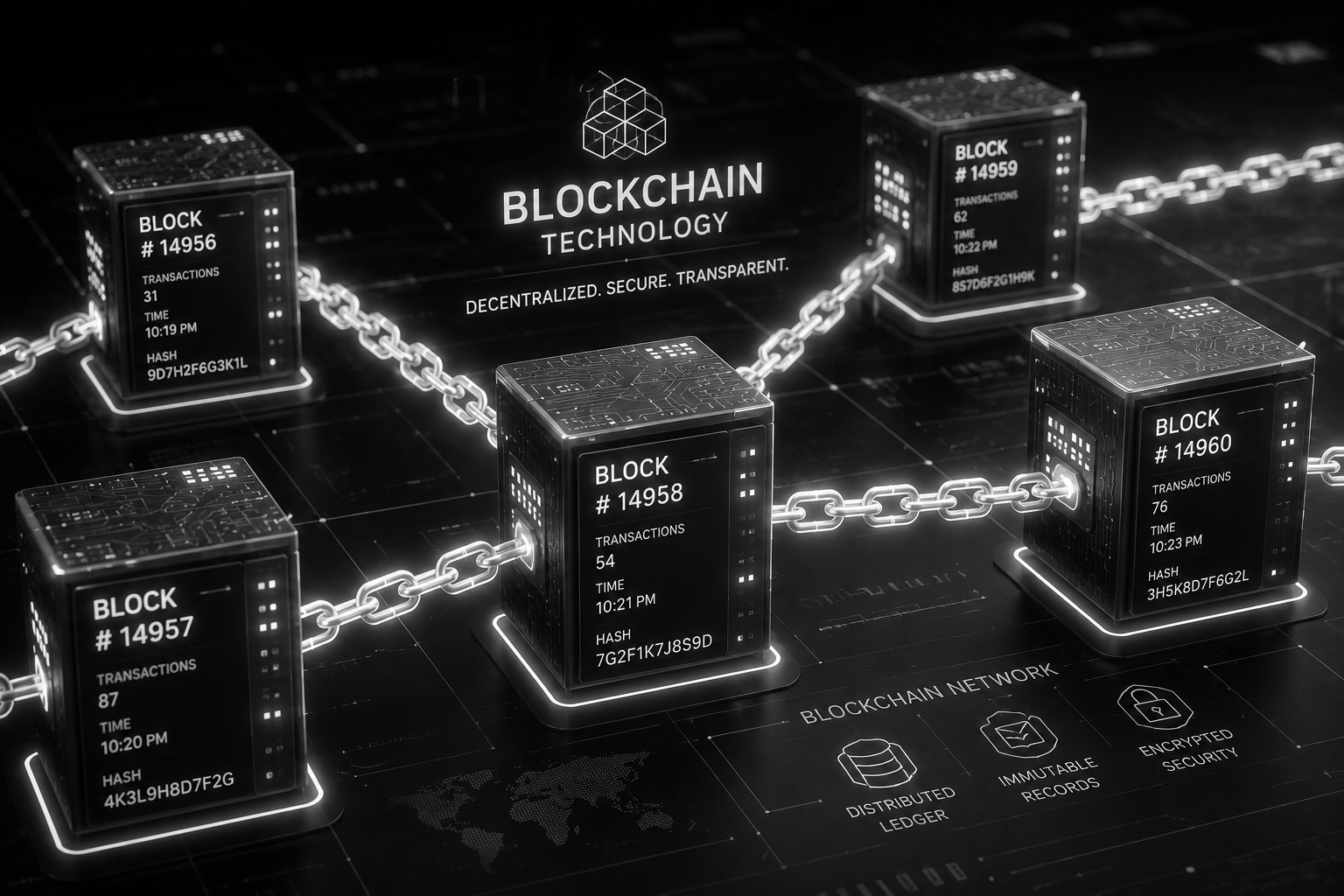
A. Tokenization Architecture
1.Token Vault
A token vault is a secure storage system that houses the mapping between the original data and its corresponding token. It ensures the integrity and confidentiality of the tokenized data. Access controls and encryption mechanisms are employed to safeguard the token vault.
2. Tokenization Process Flow
The tokenization process involves several steps. Firstly, sensitive data is securely received and transmitted to the tokenization system. The system then generates a unique token and stores it in the token vault. During subsequent transactions or data retrieval, the token is utilized for validation and decryption.
B. Integration Considerations
1.Compatible Systems and Platforms
Organizations implementing sprint tokenization must assess their existing systems and ensure compatibility with the chosen tokenization solution. Integration capabilities with payment gateways, databases, and other relevant systems should be evaluated to ensure smooth adoption and operation.
2. API Integration Options
Application Programming Interfaces (APIs) play a crucial role in integrating sprint tokenization into existing systems. Organizations should consider the availability and functionality of APIs provided by tokenization vendors. Well-documented and developer-friendly APIs simplify the integration process and promote efficient utilization of tokenization services.
C. Token Lifecycle Management
Effective management of tokens throughout their lifecycle is vital for maintaining the integrity and security of the tokenization process.
1.Token Generation
Tokens should be generated using strong cryptographic algorithms to ensure randomness and uniqueness. The token generation process should be performed securely and efficiently to support the rapid pace of transactions.
2. Token Usage and Validation
Tokens are used in place of sensitive data during transactions or data retrieval. It is crucial to implement robust validation mechanisms to ensure the authenticity and integrity of tokens. Validation processes should be quick and reliable to maintain transaction speed.
3. Token Revocation and Expiration
Token revocation and expiration mechanisms are essential for data management and security. Revoking a token renders it invalid, preventing its future use. Tokens should also have an expiration period to limit their validity and reduce the risk of unauthorized access. Proper token revocation and expiration processes must be in place to maintain data integrity.
WATCH THE VIDEO BELOW FOR MORE CLARIFICATIONS.
IV. Key Features and Functionality
A. Token Format and Structure
1.Token Composition
Sprint tokens typically consist of alphanumeric characters, ensuring a wide range of possible combinations. This enhances security by making it challenging to guess or reverse-engineer the original data from the token.
2. Token Length and Randomness
Longer tokens with high randomness provide increased security. A larger token space reduces the chances of collisions or successful token guessing attacks. Sprint tokenization employs cryptographic algorithms to generate tokens with the desired length and randomness.
B. Tokenization Algorithms and Encryption
1.Secure Token Generation
Strong cryptographic algorithms such as AES (Advanced Encryption Standard) or RSA (Rivest-Shamir-Adleman) are employed to generate sprint tokens. These algorithms ensure the generation of secure and unpredictable tokens.
2. Encryption Methods for Token Storage
The token vault, where the mapping between tokens and original data is stored, must be protected with encryption mechanisms. Encryption ensures that even if the vault is compromised, the tokens remain unreadable and unusable without proper decryption.
C. Tokenization Key Management:
1.Key Generation and Distribution
Key management plays a crucial role in sprint tokenization. Secure and random key generation is essential to maintain the confidentiality and integrity of tokens. Keys should be distributed securely to authorized parties involved in the tokenization process.
2. Key Rotation and Revocation
Regular key rotation is recommended to enhance security and mitigate the risk of compromised keys. Additionally, in case of suspected security breaches or compromised keys, a well-defined key revocation process should be in place to ensure the security of the tokenization system.
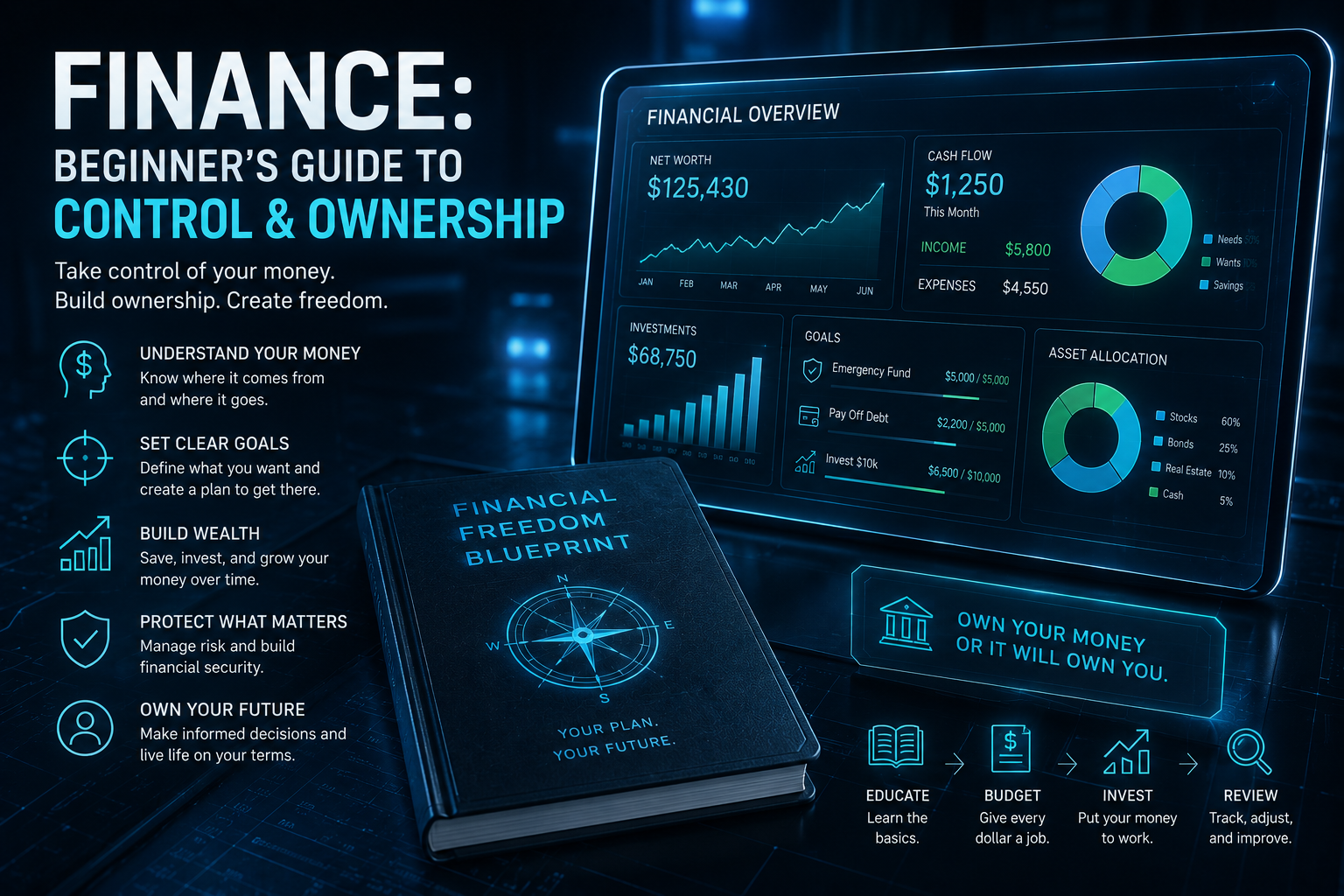
V. Use Cases and Applications
A. E-commerce and Payment Processing
Sprint tokenization is highly relevant in e-commerce and payment processing industries, where quick and secure transactions are vital. By tokenizing sensitive payment data, organizations can reduce the risk of data breaches and streamline transaction processes, leading to improved customer satisfaction and increased business efficiency.
B. Customer Data Protection
Organizations that handle customer data, such as healthcare providers or financial institutions, can leverage sprint tokenization to safeguard sensitive information. By replacing PII with tokens, organizations minimize the potential impact of data breaches and uphold customer trust.
C. Fraud Prevention and Risk Management
Sprint tokenization can be a valuable tool in fraud prevention and risk management strategies. By tokenizing valuable data, such as credit card information, organizations can reduce the risk of fraudulent activities. Even if the tokenized data is compromised, it holds no intrinsic value, rendering it useless to malicious actors.
D. Compliance with Industry Standards
Sprint tokenization helps organizations meet compliance requirements such as the PCI DSS, GDPR, and other industry-specific data protection standards. By implementing sprint tokenization, organizations can ensure they adhere to regulations regarding the protection of sensitive data. This not only avoids penalties and legal repercussions but also demonstrates a commitment to data privacy and security.
VI. Challenges and Considerations
A. Tokenization Implementation Costs
Implementing sprint tokenization may involve upfront costs associated with acquiring and integrating the necessary technology, training employees, and modifying existing systems. Organizations should carefully evaluate the cost-benefit analysis and assess the long-term advantages of sprint tokenization in terms of security, efficiency, and compliance.
B. Impact on Legacy Systems and Processes
Organizations with legacy systems and processes may face challenges in integrating sprint tokenization seamlessly. Ensuring compatibility and minimal disruption during the implementation phase requires careful planning, testing, and potentially updating or replacing outdated systems.
C. Data Integrity and Recovery Strategies
While sprint tokenization enhances security, organizations must also have robust data integrity and recovery strategies in place. In the event of system failures, data corruption, or other unforeseen circumstances, organizations should be prepared to recover and restore tokenized data accurately.
D. Training and Awareness for Employees
Successful implementation of sprint tokenization requires educating and training employees on the new processes and technologies involved. Employees should understand the importance of tokenization, their role in maintaining data security, and how to handle tokenized data effectively.
Summary
Sprint tokenization presents a significant advancement in data protection, offering enhanced security and efficiency. By replacing sensitive data with tokens, organizations can safeguard confidential information, streamline transaction processes, and simplify compliance with industry standards. The agility and benefits of sprint tokenization make it a valuable solution for organizations across various sectors.
As organizations continue to prioritize data privacy and security, sprint tokenization emerges as a robust approach to mitigate risks, prevent data breaches, and build trust with customers. By implementing sprint tokenization and adopting best practices in token management, organizations can strengthen their data protection strategies, improve operational efficiency, and navigate the evolving landscape of data privacy and security successfully.
Latest
Blockchain
13 May 2026
Blockchain
15 Mar 2026
Blockchain
25 Feb 2026
Blockchain
21 Feb 2026