James Carter
Keep Network: Revolutionizing Privacy and Security in Blockchain

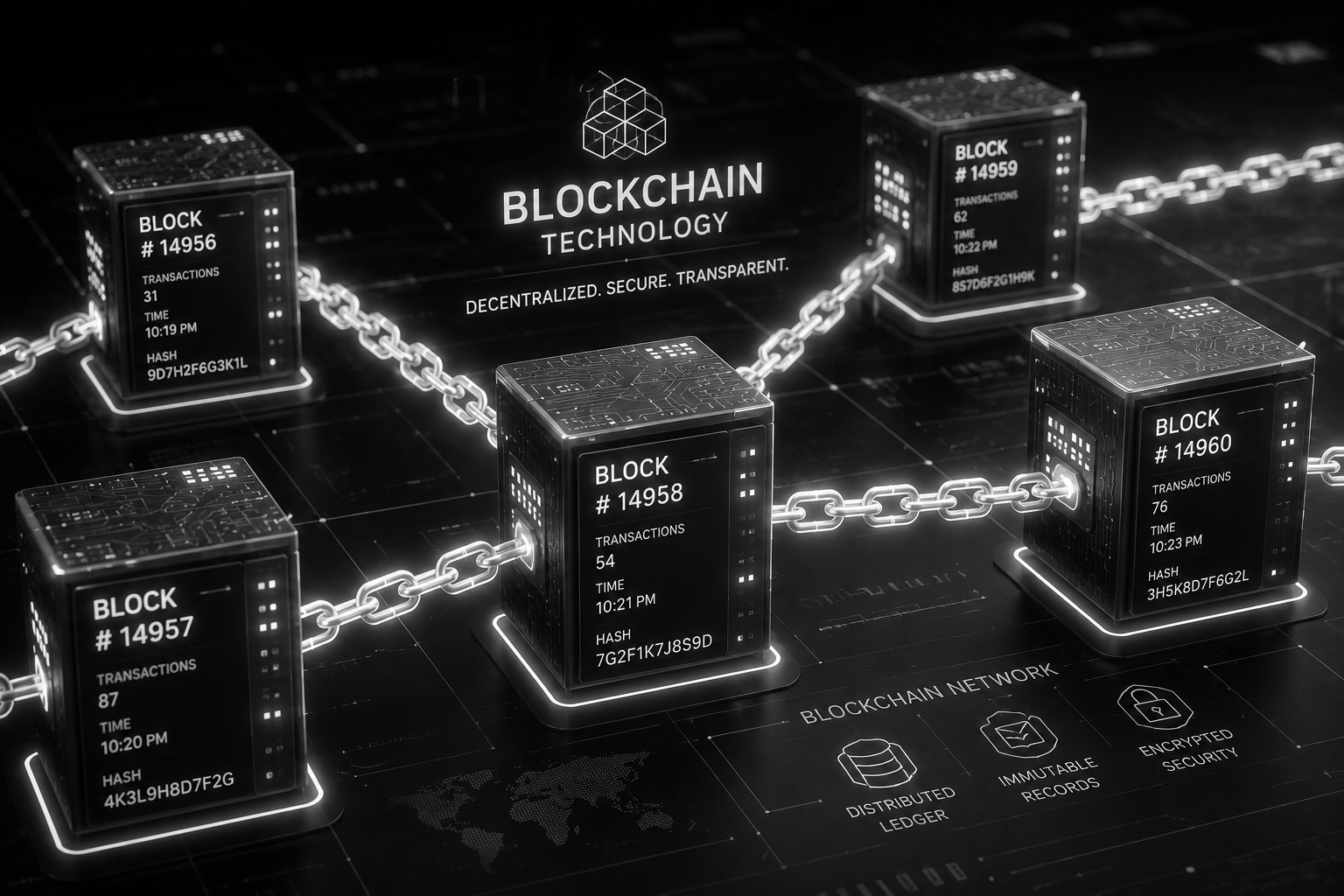
Blockchain technology has transformed various industries by offering decentralized and transparent systems. However, one critical challenge it faces is privacy and security. Keep Network emerges as a groundbreaking solution, providing a trustless and decentralized infrastructure to maintain privacy, confidentiality, and security on public blockchains. In this article, we will delve into the intricacies of Keep Network, exploring its key features, working mechanism, use cases, advantages, challenges, and future developments.
Background of Keep Network
Keep Network is a privacy and security protocol that enables the storage and utilization of private data on public blockchains. It leverages a unique combination of off-chain containers, random beacon, threshold ECDSA signatures, and decentralized keeps to ensure privacy, scalability, and interoperability within the blockchain ecosystem.
To understand the significance of Keep Networks, it is crucial to grasp the basics of blockchain technology. Blockchain is a decentralized and immutable ledger that stores transactions across multiple nodes in a networks. However, the transparent nature of public blockchains often hinders privacy and confidentiality. Keep Networks aims to address these limitations by creating a bridge between public and private data.
Key Features of Keep Network
Off-Chain Containers:
Keep Network utilizes off-chain containers called “keeps” to store private data securely. These keeps act as sealed environments where data can be stored, processed, and accessed without compromising privacy. By storing sensitive information off-chain, Keep Networks ensures that data remains hidden from the public eye while still benefiting from the security guarantees of the underlying blockchain.
Random Beacon:
The Random Beacon is a critical component of Keep Network’s security infrastructure. It generates unpredictable and unbiased randomness that is crucial for secure operations within the networks. This randomness is used for selecting keeps, assigning work, and facilitating verifications, ensuring that the system remains robust and tamper-resistant.
Threshold ECDSA Signatures:
Keep Network employs threshold ECDSA (Elliptic Curve Digital Signature Algorithm) signatures to enable secure and efficient key management. This cryptographic technique allows multiple parties to collectively sign transactions without revealing individual private keys. By distributing the signing process among multiple participants, Keep Networks achieves enhanced security while maintaining the simplicity and compatibility of standard ECDSA signatures.
tBTC and tETH Tokens:
tBTC and tETH tokens are synthetic representations of Bitcoin and Ether, respectively, within the Keep Networks ecosystem. These tokens facilitate the seamless transfer and utilization of assets between the public blockchain and the Keep Networks. By pegging these tokens to their respective underlying assets, Keep Networks enables users to leverage the benefits of private and secure transactions while still enjoying the liquidity and utility of the public blockchain.
Collaborative Security:
Keep Network embraces the concept of collaborative security, where multiple participants come together to ensure the integrity and reliability of the system. Participants include signers, stakers, and users who collectively contribute to the security and performance of the networks. This decentralized and collaborative approach reduces single points of failure, enhances resistance to attacks, and ensures the network’s continuous operation.

How Keep Network Works
Overview of the Keep Network Architecture:
Keep Networks operates as a two-layer system, with an off-chain layer and an on-chain layer. The off-chain layer consists of keeps, which store private data and perform computations, while the on-chain layer comprises smart contracts that facilitate coordination and interaction between the participants.
Steps Involved in the Keep Network Process:
Creating a Deposit:
Users initiate the process by depositing their assets (e.g., BTC or ETH) into the Keep Networks. This deposit represents the private data that needs to be stored securely and utilized on the blockchain.
Submitting a Request:
Once the deposit is made, users submit requests for specific operations to be performed on their private data within the Keep Network. These operations can include computations, data retrieval, or secure transactions.
Work Generation:
After receiving a request, the Keep Networks selects a group of keeps to perform the requested operation. The selection process utilizes the Random Beacon to ensure fairness and unbiased selection. The selected keeps collaborate to generate the required output while preserving privacy.
Work Verification:
Once the output is generated by the keeps, it undergoes a verification process to ensure its correctness and integrity. Other keeps within the networks, known as signers, validate the output and provide cryptographic proofs of its correctness.
Distributing the Result:
Upon successful verification, the result is distributed back to the user or the designated recipient on the public blockchain. The distribution mechanism guarantees the privacy of the output, ensuring that only authorized parties can access the decrypted data or utilize the processed result.
Use Cases of Keep Network
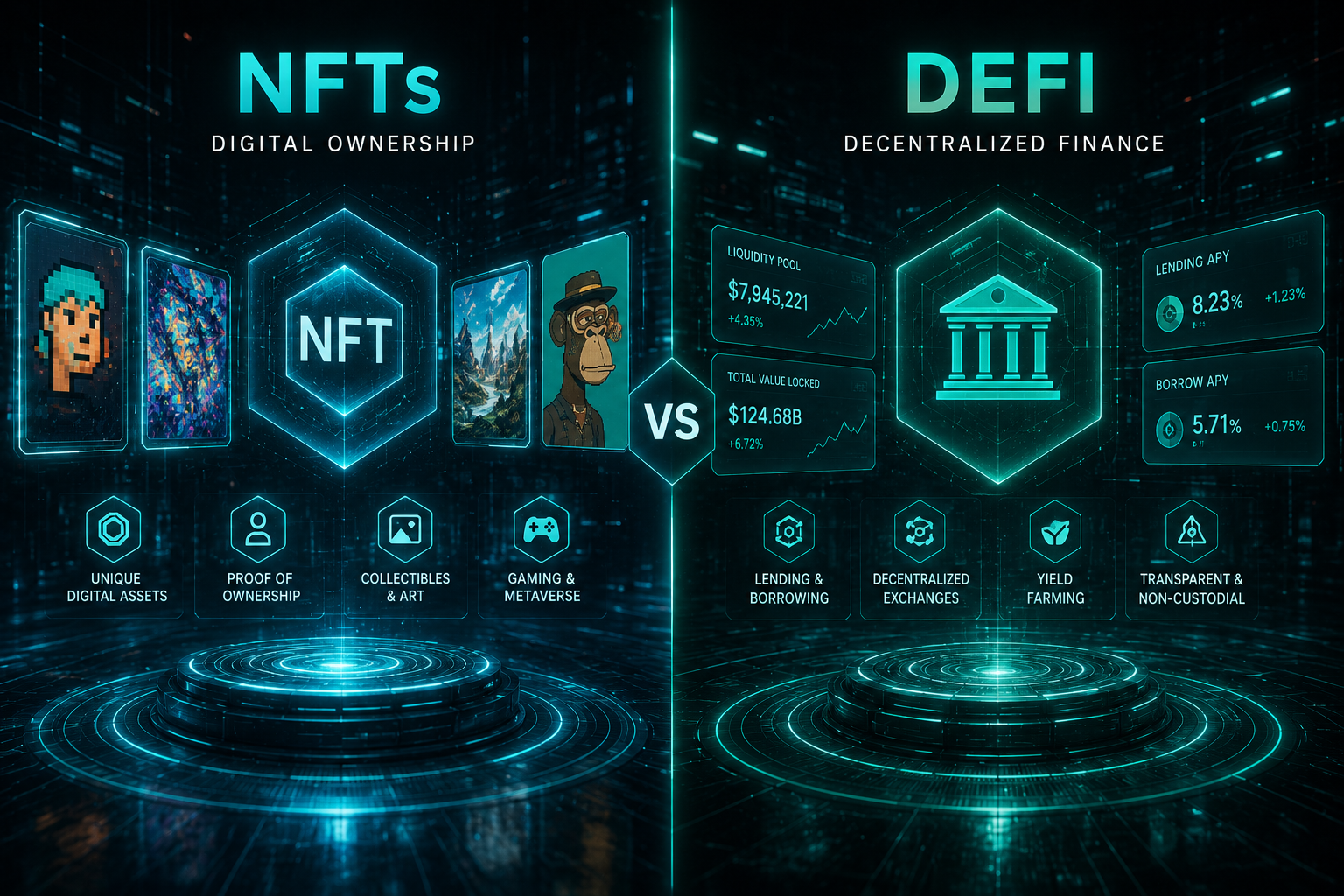
Decentralized Finance (DeFi):
Keep Network plays a crucial role in DeFi applications by enabling privacy-preserving transactions, secure lending, and decentralized asset management. Users can leverage the privacy features of Keep Networks to maintain the confidentiality of their financial activities while interacting with decentralized protocols and maintaining the benefits of the public blockchain.
Privacy-Preserving Applications:
Keep Network serves as a robust infrastructure for privacy-focused applications. It empowers developers to build decentralized applications that handle sensitive user data, such as healthcare records, identity management systems, and secure messaging platforms. Keep Networks ensures that data remains confidential and tamper-resistant while being utilized within the decentralized ecosystem.
Asset Management and Custody:
With Keep Network, users can securely store and manage their digital assets, including cryptocurrencies and non-fungible tokens (NFTs). By leveraging the privacy features, users can maintain the confidentiality of their holdings while still benefiting from the liquidity and utility of the public blockchain.
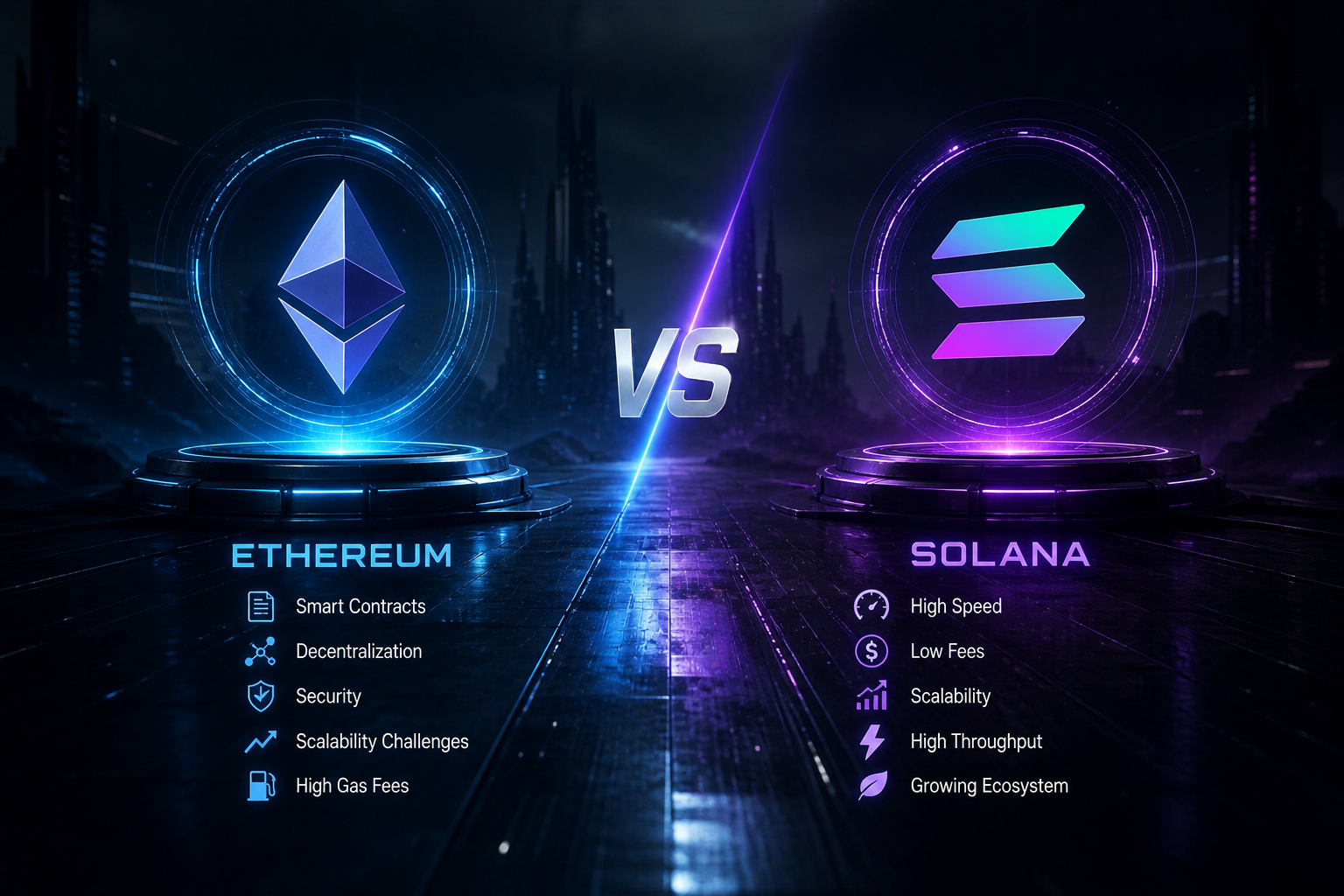
Cross-Chain Interoperability:
Keep Network acts as a bridge between different blockchains, enabling interoperability and seamless asset transfers across disparate networks. Users can securely move assets from one blockchain to another while maintaining privacy and security, opening up possibilities for cross-chain DeFi and decentralized applications.
Advantages of Keep Network
Privacy and Security:
Keep Network addresses the privacy and security challenges faced by public blockchains. By storing data off-chain and utilizing advanced cryptographic techniques, Keep Network ensures that sensitive information remains confidential, even within a public and transparent ecosystem.
Scalability and Performance:
By offloading computations and data storage to off-chain keeps, Keep Network enhances scalability and performance. The network can handle a higher volume of transactions without burdening the underlying blockchain, resulting in improved efficiency and reduced costs.
Interoperability:
Keep Network promotes interoperability between blockchains, allowing assets and data to flow seamlessly between different networks. This interoperability opens up new opportunities for collaboration and innovation across various blockchain ecosystems.
Developer-Friendly Infrastructure:
Keep Network provides a developer-friendly infrastructure with easy-to-use tools, APIs, and libraries. Developers can leverage these resources to build privacy-focused applications, seamlessly integrate with the Keep Network, and enhance the user experience while maintaining data confidentiality.
Challenges and Limitations
Adoption and Network Effects:
Like any emerging technology, Keep Network faces the challenge of adoption and establishing network effects. Widespread adoption is essential for the network’s security and performance, as a larger participant base enhances decentralization and collaboration.
Regulatory and Compliance Considerations:
Privacy-focused technologies like Keep Network need to navigate regulatory frameworks and compliance requirements. Ensuring compliance with regulations without compromising the core privacy features can be a complex task and may require collaboration with regulatory bodies.
Technical Limitations and Risks:
Keep Network, like any complex system, has technical limitations and associated risks. These can include potential vulnerabilities and exploits, scalability challenges during peak usage, and the need for continuous research and development to address emerging security concerns. It is crucial for the Keep Network team and the wider community to stay vigilant and proactive in addressing these technical limitations and mitigating associated risks.
WATCH THE VIDEO BELOW
Future Developments and Roadmap
Updates and Improvements to Keep Network:
The Keep Network team is dedicated to continuously enhancing the protocol. This includes regular updates to address security vulnerabilities, improve scalability, and introduce new features based on user feedback and market needs. Ongoing research and development efforts will ensure that Keep Network remains at the forefront of privacy and security solutions in the blockchain space.
Planned Features and Enhancements:
The roadmap for Keep Network includes several planned features and enhancements. These may include further optimizations for scalability, additional cryptographic primitives to enhance security, integrations with other blockchain networks, and improved developer tools to facilitate the creation of privacy-focused applications.
Community and Ecosystem Growth:
A strong and vibrant community is vital for the success of Keep Network. The team aims to foster community engagement, support developer initiatives, and encourage collaboration with other blockchain projects. Additionally, partnerships with industry players and strategic alliances will contribute to the growth and adoption of Keep Network.
Summary
Keep Network stands as a game-changing solution in the blockchain ecosystem, offering privacy, security, and scalability to public blockchains. By leveraging off-chain containers, threshold ECDSA signatures, random beacons, and collaborative security, Keep Network enables the storage, processing, and utilization of private data while maintaining the trustless and decentralized nature of blockchain technology.
Latest
Technology
13 May 2026
Technology
15 Mar 2026
Technology
25 Feb 2026
Technology
21 Feb 2026