Coinposters
Deconstructing Crypto Scams So You Don’t Fall For One: Expert-Verified Red Flags Every Investor Must Know

Investor Security Guide · 2026
Deconstructing Crypto
Scams So You Don’t
Fall For One:
Expert-Verified Red
Flags Every Investor
Must Know
Crypto scams are no longer clumsy, obvious traps — they are multi-month psychological operations backed by professional-grade technology, and they cost investors $17 billion in 2025 alone.
Article at a Glance
- →Crypto scammers stole approximately $17 billion in 2025 — a record-breaking year driven by AI deepfakes, pig butchering operations, and sophisticated fake platforms.
- →AI-generated deepfakes increased by 1,400% in 2025, making celebrity-endorsed crypto scams harder to detect than ever before.
- →Only about 10% of stolen cryptocurrency is ever recovered — prevention is your only real protection, and this guide gives you the tools to stay ahead.
- →39% of investment scam victims in H1 2025 were first contacted via social media — if a stranger online is pushing crypto, assume it’s a scam.
- →This expert-verified guide covers every major scam type, the red flags that expose them, and exactly how to protect yourself before a single dollar is at risk.
Table of Contents
- Crypto Scammers Stole $17 Billion in 2025 — Here Is What That Means for You
- 12 Most Dangerous Crypto Scams Targeting Investors Right Now
- 15 Red Flags Every Crypto Investor Must Know
- Social Engineering Tactics Scammers Use to Lower Your Guard
- How to Verify a Crypto Project Before You Invest a Single Dollar
- How to Protect Your Crypto Wallet From Being Drained
- What to Do Immediately If You Have Been Scammed
- Frequently Asked Questions
Crypto scams are no longer clumsy, obvious traps — they are multi-month psychological operations backed by professional-grade technology. Understanding how crypto scams operate is your first line of defense. For a comprehensive overview of crypto scams and their history, Wikipedia’s cryptocurrency scams category provides useful context. The FBI’s dedicated cryptocurrency investment fraud resource and the CFTC’s guide to spotting fraud sites are also essential reading. For investors looking to safeguard their holdings, starting with a safe crypto portfolio strategy is the essential foundation before anything else.
The blockchain is transparent, but the people exploiting it are not — and understanding how crypto scams operate is your first line of defense.
Crypto Scammers Stole $17 Billion in 2025 — Here Is What That Means for You
The numbers are staggering. According to multiple blockchain analytics firms including Chainalysis, scammers and hackers extracted approximately $17 billion from the crypto ecosystem in 2025 — a record that included the largest single cryptocurrency theft in history. The FBI reported that US citizens alone lost $9.3 billion to crypto-related fraud in 2024, with H1 2025 already adding another $939 million to that total.
What makes these figures truly alarming isn’t just the scale — it’s who is being targeted. People aged 40–49 filed the most reports (5,999 cases in H1 2025), while victims aged 60 and older suffered the highest total losses at $2.8 billion in 2024.
Crypto Scam Losses by Region — 2025 Growth Rate
| Region | Change in Losses | Trend |
|---|---|---|
| Africa | +112% | Highest increase globally |
| US & Canada | +86% | Second highest increase |
| Middle East | +79% | Rapid growth |
| Latin America | +50% | Significant increase |
| Asia-Pacific | -23% | Direct evidence that awareness works |
The Asia-Pacific region bucked the trend with a 23% decline — direct evidence that awareness and enforcement actually work. That’s exactly why understanding these crypto scams matters.
12 Most Dangerous Crypto Scams Targeting Investors Right Now
Not all crypto scams are created equal. Some are quick and opportunistic; others are elaborate, months-long operations designed to build genuine emotional trust before stealing everything. Here are the twelve most damaging scam types you need to recognize on sight.
1. Pig Butchering Scams: The Long Con That Costs Victims Everything
Pig butchering — known as sha zhu pan in Chinese — is the most financially devastating scam type operating today. The playbook is consistent: a stranger contacts you through social media, WhatsApp, or a dating app, builds a friendship or romantic connection over weeks or months, then casually introduces a “can’t-miss” crypto investment platform. The platform shows fake profits, encourages larger deposits, and then vanishes entirely when you try to withdraw. The FBI notified more than 4,300 pig butchering victims in 2025 alone. The Chainalysis 2025 report noted that 76% of pig butchering victims did not realize they were being scammed while it was happening — because the relationship felt completely real.
2. Rug Pulls: When Developers Drain the Pool and Disappear
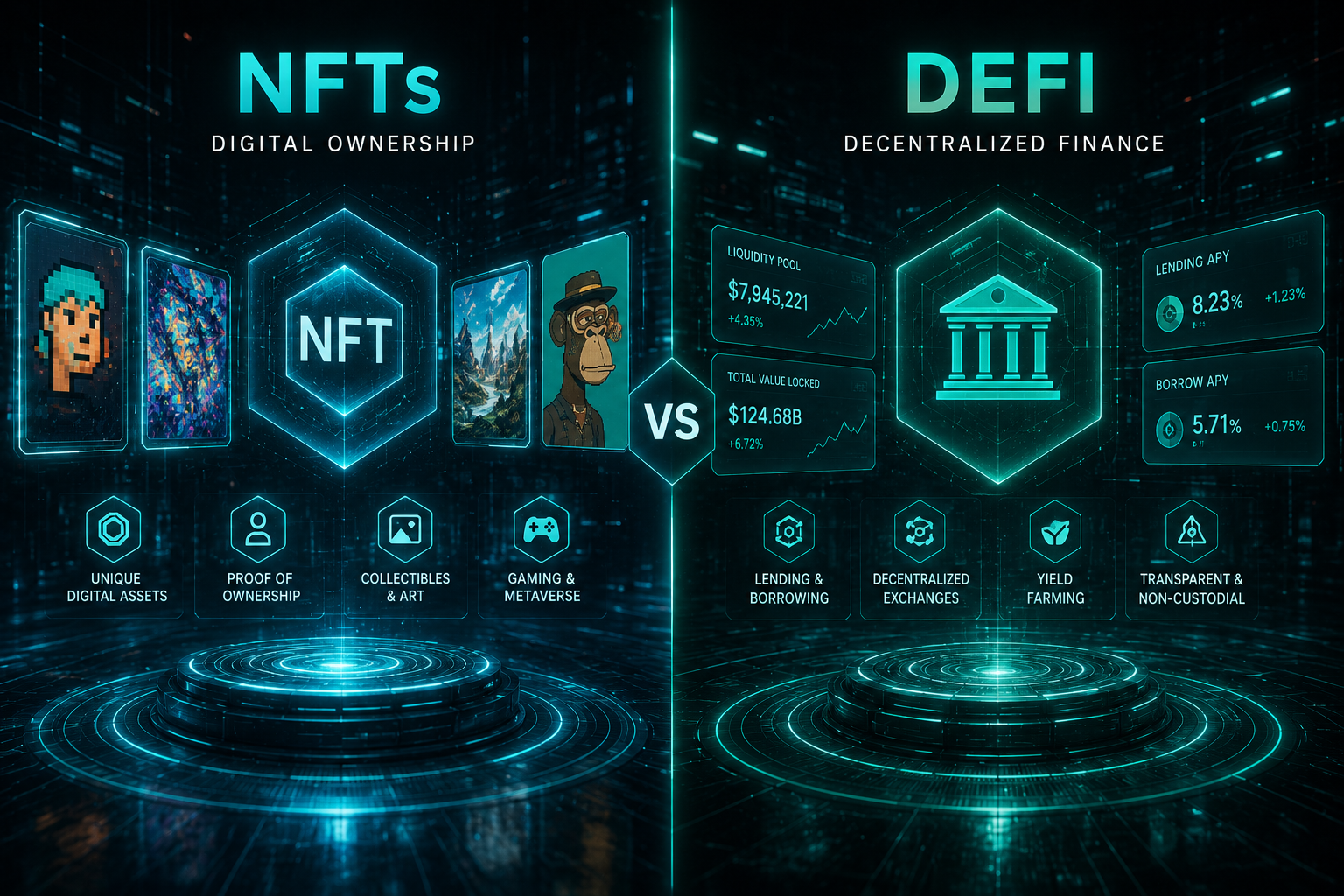
A rug pull happens when a project team builds enough hype and liquidity around a new token, then pulls all funds from the liquidity pool and disappears. These crypto scams are particularly dangerous in the DeFi space because smart contracts can be coded with hidden backdoors that only the developers can trigger. The signs are almost always there in advance: anonymous teams, no audited smart contracts, and whitepapers that borrow heavily from existing legitimate projects.
3. AI Deepfake Giveaway Scams: Fake Celebrities, Real Losses
AI deepfake usage in crypto scams increased by 1,400% in 2025. Scammers create highly convincing video content featuring Elon Musk, Vitalik Buterin, and other well-known figures apparently endorsing a crypto giveaway — send us 1 BTC, get 2 BTC back. The videos are broadcast through hacked YouTube channels, fake social media accounts, and paid ads. No legitimate giveaway ever requires you to send crypto first.
4. Fake Crypto Exchanges: Platforms Built to Steal Your Deposit
These platforms mirror legitimate exchanges with professional-looking interfaces, customer support chatbots, and even fake trading activity on the screen. They allow small test withdrawals to build confidence, then freeze accounts the moment a significant deposit lands. Always verify an exchange is registered with relevant financial regulators — in the US, check FinCEN; in the UK, the FCA; in Australia, ASIC.
5. Address Poisoning: The Copy-Paste Trap Most Investors Never See Coming
Address poisoning is devastatingly simple. A scammer sends a tiny transaction — sometimes $0.00 — from a wallet address that closely mimics one you’ve previously interacted with. When you copy your transaction history to send funds again, you accidentally copy the scammer’s look-alike address instead of the correct one. Always verify the full wallet address character by character, never just the first and last few digits. For additional security, consider using a hardware wallet vs software wallet to protect your assets.
6. Phishing Attacks: Fake Emails and Sites Designed to Steal Your Login
Phishing emails impersonating Coinbase, MetaMask, Ledger, and Binance are sent by the millions every month. They direct you to pixel-perfect fake login pages designed to capture your credentials or seed phrase the moment you enter them. Always navigate to exchanges by typing the URL manually, never through email links — and check for subtle domain misspellings like “coinbasse.com” or “metamask-support.io.” To understand more about how these attacks work, consider reading about mobile wallet vs. desktop wallet security.
7. SIM Swap Attacks: How Scammers Hijack Your Phone Number
A SIM swap attack involves a scammer convincing your mobile carrier to transfer your phone number to a SIM card they control. Once they have your number, they can intercept SMS-based two-factor authentication codes and take over any account linked to that number. This is precisely why SMS-based 2FA is a security liability — authenticator apps like Google Authenticator or Authy are significantly safer alternatives.
8. Fake Airdrops: Free Tokens That Empty Your Wallet
You wake up to find unfamiliar tokens sitting in your wallet. Interacting with them — even just trying to swap or transfer them — triggers a malicious smart contract that drains your wallet of its legitimate assets. The rule is simple: never interact with tokens you did not explicitly request, regardless of how valuable they appear on-screen.
9. Pump and Dump Schemes: Coordinated Hype With One Exit
Coordinated groups — often operating in private Telegram channels — accumulate a low-liquidity token, then flood social media with hype to inflate the price. Retail investors pile in, the organizers dump their holdings at the peak, and the price collapses within hours. Low-cap tokens with sudden explosive social media momentum and no underlying development activity are the clearest warning sign.
10. Romance Scams: Emotional Manipulation as a Financial Weapon
Distinct from pig butchering only in that the financial ask may come much later, romance scams build deep emotional bonds before introducing a financial crisis — a medical emergency, a stuck inheritance, a business opportunity. The request for crypto transfers comes once trust is fully established. According to the FBI, 39% of investment scam victims in H1 2025 were first contacted via social media, and romance-based approaches dominate that category.
11. Fake Recovery Services: Scammers Who Target Previous Victims
This is among the cruellest scam types in operation. After someone loses money to a crypto fraud, fake recovery services appear — through Google ads, forums, or direct outreach — promising to retrieve stolen funds for an upfront fee. The Chainalysis 2025 report documented cases where victims lost an additional $100,000 or more to fake recovery operators after an initial scam. No legitimate service can reliably recover stolen crypto from a confirmed scam.
12. Malicious Smart Contracts: Code Written to Drain Your Wallet
When you interact with a DeFi protocol or NFT mint, you often sign a transaction granting that contract permission to move tokens from your wallet. Malicious contracts exploit those approvals — sometimes immediately, sometimes weeks later. Every approval you sign is a potential exposure point. To safeguard your assets, consider using secure options like a mobile or desktop wallet for better control over your transactions.
Malicious Smart Contract — Protection Rules
- ◆Always read what permissions a transaction is requesting before signing
- ◆Use Revoke.cash regularly to audit and remove unnecessary token approvals
- ◆Treat unknown contracts the same way you’d treat an unknown executable file on your computer
- ◆Check contract audit status on Etherscan before interacting with any new DeFi project
15 Red Flags Every Crypto Investor Must Know
Spotting crypto scams before they cost you money comes down to pattern recognition. These fifteen red flags appear repeatedly across every scam type — train yourself to stop at the first one you see.
1. Guaranteed Returns With Zero Risk
No legitimate investment — in crypto or any other asset class — can guarantee returns. Crypto markets are volatile by definition. Any platform, person, or project that promises fixed daily, weekly, or monthly returns is either running a Ponzi scheme or outright lying. The more specific the guarantee — “earn 3% daily” or “double your BTC in 30 days” — the more certain you can be it is a scam. For more insights on investment strategies, consider the differences between hodling vs active trading in the crypto market.
2. Anyone Asking for Your Seed Phrase or Private Keys
“There is no legitimate reason — not technical support, not account verification, not wallet recovery — for any person, platform, or application to ever ask for your seed phrase. The moment someone asks, the conversation is over. Not suspicious. Over.”
Your seed phrase is the master key to your entire wallet. There is no legitimate reason — not technical support, not account verification, not wallet recovery — for any person, platform, or application to ever ask for it. The moment someone asks for your seed phrase or private keys, the conversation is over. Not suspicious. Over.
3. Urgency Tactics Designed to Stop You From Thinking Clearly
Scammers engineer time pressure because careful thinking is their biggest enemy. Phrases like “this offer closes in 2 hours,” “only 3 spots remaining,” or “you’ll lose your position if you don’t act now” are psychological weapons designed to bypass your rational decision-making. Legitimate investment opportunities do not expire in hours.
The urgency is always manufactured. Real blockchain projects, regulated exchanges, and credible DeFi protocols do not cold-contact investors with countdown timers. If you feel rushed, that pressure itself is the red flag — slow down, and the scam almost always reveals itself.
4. Anonymous or Unverifiable Project Teams
Satoshi Nakamoto’s anonymity is the exception, not the rule — and it’s an exception scammers exploit constantly. When a project’s founders, developers, or advisors cannot be verified through LinkedIn profiles, on-chain contribution history, GitHub activity, or prior industry presence, you have no accountability structure whatsoever. If the team disappears with the funds, there is nobody to identify, pursue, or prosecute. Always cross-reference team members across multiple platforms before committing any capital.
5. Unsolicited Investment Advice From Strangers Online
Nobody with a genuinely profitable trading strategy needs to share it with a stranger on Telegram, Instagram, or a dating app. When someone you have never met steers a conversation toward a specific crypto platform or investment opportunity, treat it as a pig butchering approach until proven otherwise. The FBI confirmed that 39% of investment scam victims in H1 2025 were first reached through social media platforms.
6. Withdrawal Fees That Appear After Your Money Is Already In
This is a hallmark of fake exchange crypto scams. The platform shows impressive returns on your investment, but when you attempt to withdraw, a sudden “tax fee,” “compliance fee,” or “liquidity unlock fee” appears — always payable upfront in crypto. Paying it produces another fee. Legitimate platforms deduct fees from your balance; they never require additional deposits to release funds you supposedly already own.
7. Platforms With No Verifiable Regulatory Registration
Every legitimate cryptocurrency exchange operating in a major market is registered with a financial regulator. In the US, check FinCEN’s MSB registrant search. In the UK, use the FCA register. In Australia, verify through ASIC. In the EU, look for MiCA compliance disclosures. If a platform cannot produce a verifiable registration number that matches a real entry in one of these databases, it is operating outside the law — and your funds have no protection.
Scam platforms often list fake registration numbers, fabricated licenses, or vague references to offshore jurisdictions with minimal oversight. A registration claim is meaningless unless you verify it yourself through the official regulator’s website — not through a link the platform provides.
8. Whitepapers That Are Vague, Copied, or Do Not Exist
A whitepaper is a project’s technical and economic blueprint. It should explain the problem being solved, the technology underpinning the solution, the tokenomics, and the roadmap in specific, verifiable terms. Legitimate projects publish whitepapers that invite technical scrutiny — because they can withstand it.
Scam whitepapers follow recognizable patterns. They are heavy on abstract language about “revolutionizing finance” and “next-generation blockchain solutions” but light on actual technical architecture. Some are partially or entirely plagiarized from legitimate projects, with names swapped out.
How to Evaluate a Whitepaper — Quick Checklist
- ◆Run sections through a plagiarism checker like Copyscape
- ◆Look for specific technical details: consensus mechanism, token supply logic, smart contract architecture
- ◆Check whether the roadmap contains verifiable past milestones or only future promises
- ◆Search for the whitepaper’s content on GitHub — legitimate projects have active, public repositories
9. Social Media Accounts Flooded With Suspicious Five-Star Reviews
Scam projects purchase fake reviews, fabricate testimonials, and flood comment sections with bot accounts praising the platform. Watch for reviews that use generic, non-specific language (“great returns,” “trusted platform,” “highly recommend”), accounts created within the last few months, and comment sections where critical questions are deleted or met with hostile responses from suspiciously new accounts.
10. Token Contracts Not Listed on CoinGecko or CoinMarketCap
If someone is promoting a token that doesn’t appear on CoinGecko or CoinMarketCap, that absence is significant. While new legitimate tokens do exist before listing, scammers frequently push unlisted contracts because there is no independent price tracking, no liquidity transparency, and no community accountability. Always paste the contract address directly into CoinGecko or Etherscan to verify what you’re actually being asked to buy. For additional research, consider using some of the best crypto research platforms to gain more insights.
11. Websites Registered Within the Last Few Months
Domain age is a fast, free, and reliable scam signal. Use a WHOIS lookup tool — try whois.domaintools.com or icann.org/lookup — and check the registration date of any platform asking for your money. Scam operations spin up new domains constantly because old ones get flagged and blacklisted.
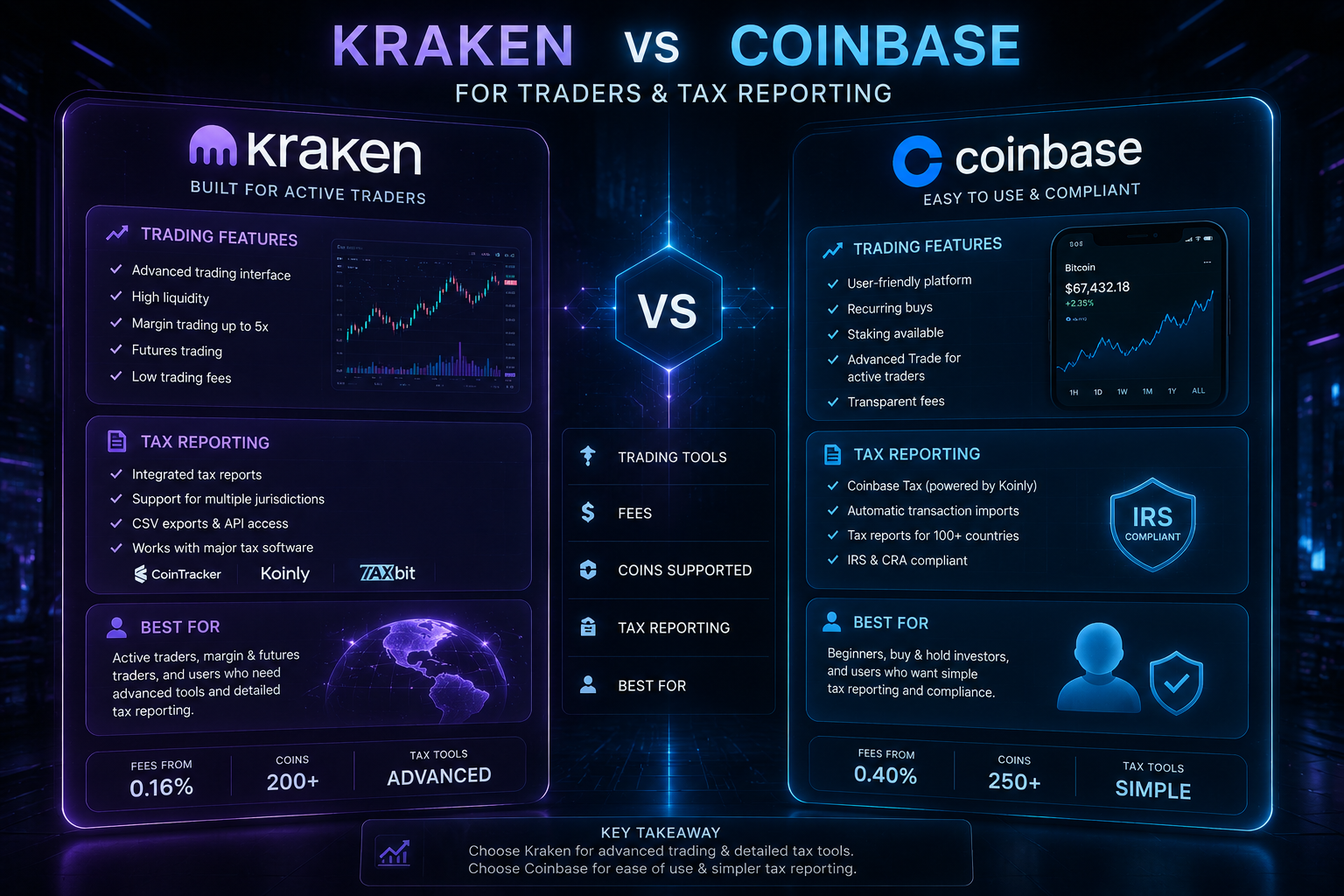
A platform claiming to have “served over 500,000 investors since 2018” but with a domain registered in late 2024 is lying about its history. Established exchanges like Coinbase, Kraken, and Binance have domain registration histories stretching back well over a decade.
Also look at the registrar details. Scam sites frequently use privacy-protected registrations that hide the owner’s identity entirely, which legitimate businesses operating in regulated markets rarely need to do.
12. Promises of Exclusive or Early Access Opportunities
The word “exclusive” triggers a cognitive bias called fear of missing out — and scammers know exactly how to weaponize it. Being told you have been “specially selected” for an investment opportunity, or that you’re getting access to a pre-sale before the general public, creates a false sense of privilege that clouds judgment.
Legitimate early-access opportunities in crypto do exist — but they come through verifiable channels: official project websites, known launchpads like Binance Launchpad or Coinlist, or established VC relationships. They do not arrive via unsolicited DMs from strangers.
Before Acting on Any “Exclusive” Opportunity
- ◆Verify any pre-sale through the project’s official website and social channels independently
- ◆Check whether the launchpad hosting the pre-sale has a legitimate track record
- ◆Look for independent coverage from established crypto media outlets like CoinDesk or The Block
- ◆Be especially skeptical if the opportunity came through a personal referral from someone you only know online
Scarcity and exclusivity are sales mechanisms. When they appear in unsolicited investment pitches, they are manipulation mechanisms.
13. Celebrity Endorsements You Cannot Verify Through Official Channels
With AI deepfakes increasing by 1,400% in 2025, a convincing video of a celebrity endorsing a crypto project is no longer difficult to fabricate. Before taking any celebrity endorsement seriously, verify it through the celebrity’s official verified social media accounts, their official website, and credible media coverage. If the endorsement only exists on the platform promoting the investment, it almost certainly does not exist at all.
14. Pressure to Recruit Others for Rewards
Any crypto platform that offers you bonuses, tokens, or higher returns in exchange for referring friends and family is using a pyramid structure — regardless of what it calls itself. This model is unsustainable by mathematical definition and requires a constant flow of new victims to pay existing participants. The people at the top extract the most; everyone else eventually loses. Multi-level referral structures have no place in a legitimate investment platform.
15. Platforms That Let You See Profits But Block All Withdrawals
This is the final and most financially devastating trap. Scam platforms allow small test withdrawals specifically to build your confidence and encourage larger deposits. Once a significant amount is in the account, every withdrawal attempt is met with a new excuse: account verification delays, regulatory holds, tax compliance requirements, or liquidity processing times. The dashboard showing your growing balance is fake. The profits are numbers on a screen controlled entirely by the scammer. Once you understand this mechanic, the pattern becomes visible across dozens of different scam platforms operating under different names.
Social Engineering Tactics Scammers Use to Lower Your Guard
Technical red flags are only half the picture. The most financially damaging crypto scams don’t succeed because of sophisticated technology — they succeed because of sophisticated psychology. Social engineering is the practice of manipulating human behavior rather than exploiting technical vulnerabilities, and in 2025, it is the primary weapon in a crypto scammer’s arsenal.
Understanding these psychological tactics doesn’t make you immune to them — cognitive biases are hardwired into human decision-making. But awareness creates a measurable delay between stimulus and response, and that delay is often enough to stop a scam in its tracks.
How Scammers Build False Trust Over Weeks or Months
The most effective crypto scammers don’t ask for money immediately. They invest time — sometimes weeks, sometimes months — building what feels like a genuine relationship before a single dollar is ever mentioned. This is the defining characteristic of pig butchering and romance scams, and it’s what makes them so psychologically effective.
How Scammers Build False Trust — The Playbook
- ◆Regular daily contact that mirrors the rhythm of a real friendship or relationship
- ◆Sharing personal details, photos, and life stories (often fabricated but internally consistent)
- ◆Demonstrating apparent expertise in crypto to establish credibility before any pitch
- ◆Allowing the victim to make the first small investment independently — making it feel like their own decision
- ◆Celebrating small “wins” together to create shared emotional investment in the platform
What makes this approach so effective is that by the time the financial pitch arrives, it doesn’t feel like a pitch. It feels like a trusted friend sharing an opportunity. The victim’s own emotional investment in the relationship becomes the mechanism of the scam.
Scammers operating pig butchering operations often work in organized, overseas criminal compounds — operations documented extensively by the UN Office on Drugs and Crime in Southeast Asia. These are not lone actors; they are trained operatives following scripted playbooks optimized through thousands of previous victim interactions.
The practical defense is blunt but effective: maintain a firm personal rule that no investment recommendation from someone you have only met online — regardless of how long you have been talking — will be acted upon without independent, offline verification.
The Psychology Behind Manufactured Urgency and Exclusivity
Common Scammer Urgency Scripts — Decoded
| What the Scammer Says | What It Actually Means |
|---|---|
| “This pre-sale closes in 3 hours” | There is no pre-sale — the timer resets for every victim |
| “Only 5 slots left at this rate” | Artificial scarcity designed to trigger FOMO |
| “My insider contact can only hold this until tonight” | There is no insider — urgency is manufactured on demand |
| “Withdraw from Coinbase now before the window closes” | Moving you away from a regulated platform to an unregulated scam one |
| “I’m sharing this with you because I trust you — don’t tell others” | Isolation tactic to prevent you from seeking outside opinions |
Manufactured urgency exploits two well-documented cognitive biases: scarcity bias (we value things more when they appear limited) and loss aversion (the pain of missing out is psychologically stronger than the pleasure of gaining). Scammers don’t need a psychology degree to weaponize these biases — they learn from experience which scripts produce results.
The isolation tactic — “don’t tell others about this opportunity” — is particularly dangerous. It is specifically designed to prevent you from consulting friends, family, or financial advisors who might identify the scam immediately. Any investment opportunity that requires secrecy is an investment opportunity you should walk away from without hesitation.
A simple personal rule neutralizes most urgency tactics: any investment that cannot wait 48 hours for you to conduct independent research is an investment you do not make. Legitimate opportunities exist on a timeline that accommodates due diligence.
Why 76% of Pig Butchering Victims Did Not Know They Were Being Scammed
The Pig Butchering Timeline: How Crypto Scams Operate
| Phase | Duration | What Happens |
|---|---|---|
| Initial Contact | Day 1–3 | Friendly, non-financial approach via social media, dating app, or “wrong number” text |
| Relationship Building | Weeks 1–6 | Daily contact, shared personal stories, establishment of trust and emotional connection |
| Crypto Introduction | Weeks 4–8 | Casual mention of personal crypto success — not a pitch, just a lifestyle detail |
| First Investment | Weeks 6–10 | Victim encouraged to try a small deposit — often successful withdrawal allowed to build confidence |
| Escalation | Months 2–5 | Larger deposits encouraged; fake profits displayed; withdrawal barriers begin appearing |
| The Exit | Final stage | Platform disappears or freezes; scammer cuts contact; funds are gone |
The Chainalysis 2025 report’s finding that 76% of pig butchering victims didn’t know they were being scammed while it was happening is not a statement about intelligence — it is a statement about how expertly these operations are designed. Victims aren’t fooled because they’re naive; they’re fooled because the scam is engineered specifically to exploit the neural pathways of human trust and emotional bonding.
By the time the financial component is introduced, the victim has already formed a genuine emotional attachment. Refusing the investment pitch doesn’t just feel like declining a trade — it feels like rejecting a friend. That emotional friction is the entire point of the months-long groundwork.
The most effective protection against pig butchering is a personal policy of never acting on investment advice from anyone you have not met in person and verified in the physical world — regardless of how long you have communicated online, how genuine the relationship feels, or how compelling the opportunity appears.
How to Verify a Crypto Project Before You Invest a Single Dollar
Due diligence in crypto is not optional — it is the difference between building wealth and losing it. The tools available to verify a project’s legitimacy are free, accessible, and require no technical expertise to use. What follows is a practical, step-by-step framework you can apply to any project before committing a single dollar.
How to Check Smart Contract Legitimacy on Etherscan
Etherscan is your most powerful free tool for evaluating any Ethereum-based contract before you interact with it. Go to etherscan.io, paste the contract address into the search bar, and look for three things immediately: whether the contract code is verified (a green checkmark next to “Contract”), how long the contract has been deployed, and whether the transaction history shows organic activity or suspiciously uniform deposits.
A verified contract means the source code has been made public and matches the deployed bytecode — scam contracts frequently remain unverified because transparency would expose their malicious functions. Also check the “Token Holders” tab: if more than 50% of the token supply is held by a single wallet or a small cluster of wallets, that’s a significant rug pull warning signal.
Etherscan Contract Verification — What to Look For
- ◆Look for a third-party audit badge from firms like CertiK, Hacken, or Trail of Bits
- ◆Check the contract’s age — contracts deployed within the last 30 days carry higher risk
- ◆Review the “Write Contract” functions for anything labeled “drain,” “sweep,” or with obfuscated function names
- ◆Use Token Sniffer (tokensniffer.com) for an automated scam score on any ERC-20 token
How to Use WHOIS to Expose Freshly Created Scam Websites
A WHOIS lookup takes under 60 seconds and can immediately expose a platform that is lying about its history. Navigate to lookup.icann.org or whois.domaintools.com, enter the platform’s domain name, and check the “Creation Date” field. A platform claiming years of operation but with a domain registered in the last six months is misrepresenting itself — full stop.
Beyond domain age, look at the registrar details. Legitimate financial platforms operating in regulated markets almost never use privacy-protected registration services that completely mask the owner’s identity. Pay attention to the registrant country as well — a platform claiming to be a US-registered exchange but with a domain registered through a registrar in an unrelated jurisdiction with no traceable ownership is a significant warning sign.
How to Confirm a Team’s Identity Through LinkedIn and On-Chain Data
Start with LinkedIn — search each named team member individually and look for a profile history that predates the project by several years. A developer who supposedly has a decade of blockchain experience but whose LinkedIn account was created six months ago is almost certainly a fabricated identity. Look for mutual connections, endorsements from independently verifiable people, and a timeline of employment that holds up to scrutiny.
Cross-reference the team’s GitHub activity next. Legitimate developers leave a public trail of commits, repositories, and contributions to open-source projects. A founding developer with no verifiable GitHub history in a space that is fundamentally built on open-source code is a serious red flag.
For on-chain verification, check whether team wallet addresses identified in the tokenomics section actually show vesting schedules being honored. Scam teams frequently allocate large token percentages to themselves with no lock-up period — meaning they can dump their holdings the moment the token launches.
Team Identity Verification — Four-Point Check
- ◆Search the team member’s name alongside “crypto scam” or “rug pull” to surface prior incidents
- ◆Verify speaking engagements, podcast appearances, or conference presentations they claim on LinkedIn
- ◆Check whether their Twitter/X accounts have authentic engagement histories or follower counts that jumped suddenly
- ◆Use DeFiLlama to confirm whether the project’s TVL data matches what they claim publicly
If the team checks out across LinkedIn, GitHub, and on-chain data independently — not just through links the project itself provides — that’s a meaningful positive signal. No single verification is conclusive, but a team that withstands scrutiny across multiple independent channels is operating very differently from one that evaporates the moment you look closely.
How to Protect Your Crypto Wallet From Being Drained
Knowing how to spot crypto scams is one layer of protection. Having a wallet architecture that limits your exposure even if something slips through is the layer that actually keeps your assets safe when it matters most.
Why You Need Separate Hot, Cold, and Burner Wallets
A single wallet that holds all your crypto and interacts with every platform you use is the highest-risk configuration possible. One malicious contract approval, one phishing page, one compromised browser extension — and everything is gone in a single transaction. The solution is wallet segmentation, and it costs nothing to implement.
The Three-Wallet Security Architecture
Cold Wallet
Hardware wallet (Ledger Nano X or Trezor Model T). Holds the bulk of assets. Never connects directly to DeFi platforms or exchanges.
Hot Wallet
Holds only what you’re actively trading. An amount you could afford to lose without catastrophic consequences.
Burner Wallet
Fresh address used specifically for interacting with new, unverified contracts or claiming airdrops. If drained, main holdings are untouched.
How to Safely Handle Mystery Tokens That Appear in Your Wallet
When unfamiliar tokens appear in your wallet without any action on your part, treat them as active threats rather than pleasant surprises. These are almost always airdrop scam setups: the token’s smart contract is coded so that any interaction — attempting to swap, transfer, or even approve the token — triggers a function that drains your legitimate assets.
The correct approach is to simply ignore them. Do not attempt to sell them on a DEX, do not try to transfer them, and do not click any website links associated with the token’s contract page. If you want to clean up your wallet view, most wallet interfaces allow you to hide tokens without interacting with them — use that option. The tokens are worthless. The trap is only triggered if you engage.
Authenticator Apps vs. SMS Two-Factor Authentication: Why It Matters
SMS-based two-factor authentication is better than no 2FA at all — but it is a known security liability in the crypto space. A successful SIM swap attack, which requires only a social engineering call to your mobile carrier, hands an attacker every SMS-based authentication code tied to your phone number. SIM swaps have been used to drain six-figure and seven-figure crypto accounts in documented cases across the US and UK.
Authenticator apps like Google Authenticator, Authy, or Aegis (for Android) generate time-based one-time passwords locally on your device, with no reliance on your phone number or carrier infrastructure. An attacker who successfully SIM swaps your number gets nothing useful if your 2FA is authenticator-based rather than SMS-based.
For exchanges holding significant balances, go one step further with a hardware security key like the YubiKey 5 Series. This is a physical USB or NFC device that must be physically present to authenticate a login — making remote account takeover essentially impossible regardless of whether your password or phone number is compromised. For more on crypto security, consider the differences between a hardware wallet and a software wallet.
Migrating From SMS to Authenticator 2FA — Do This Now
- ◆Switch every crypto exchange account from SMS 2FA to an authenticator app immediately
- ◆Back up your authenticator app’s recovery codes in a secure, offline location
- ◆Contact your mobile carrier and request a SIM lock or port freeze on your account
- ◆Never store 2FA recovery codes in email, cloud notes, or anywhere accessible from a connected device
How to Audit and Revoke Token Approvals With Revoke.cash
Every time you interact with a DeFi protocol, you likely granted that protocol permission to move tokens from your wallet — and most people never revoke those permissions after the transaction is complete. Over time, a wallet that has been active for a year or more accumulates dozens of open approvals, each one a door that a malicious contract could walk through if the underlying protocol is later exploited. Go to Revoke.cash, connect your wallet in read-only mode, and review every active approval listed. Revoke anything you don’t recognize, anything connected to a project you no longer use, and any approval granting an unlimited spending allowance — always set approvals to the exact amount needed for a specific transaction rather than unlimited.
What to Do Immediately If You Have Been Scammed
“The most important immediate action is to stop sending any more funds, regardless of what the scammer tells you about fees, taxes, or unlock requirements. Every additional payment makes the total loss larger.”
CoinPosters · Investor Security Guide 2026
Discovering you’ve been the victim of crypto scams is a disorienting, often devastating experience — and the emotional shock of it is exactly what scammers count on to delay your response. The faster you act in the hours immediately following a scam, the marginally better your chances of limiting further damage, even if full recovery is unlikely.
The most important immediate action is to stop sending any more funds, regardless of what the scammer tells you about fees, taxes, or unlock requirements. Every additional payment made after the initial theft makes the total loss larger and the recovery probability smaller. Sever the financial relationship completely, even if cutting it off means accepting a painful loss.
First Steps in the 24 Hours After a Crypto Scam
Your first priority is documentation. Screenshot every conversation, transaction record, wallet address, platform URL, email correspondence, and any other evidence before it disappears — scammers delete accounts and platforms rapidly once a victim becomes unresponsive to further payment requests.
First 24 Hours After a Crypto Scam — Action Steps
- Stop all further transactions — do not send any more funds for any reason
- Document everything immediately — screenshots of conversations, transaction IDs, wallet addresses, and platform details
- Revoke any token approvals connected to the scam platform using Revoke.cash
- Transfer remaining assets from any compromised wallet to a fresh, unconnected wallet address
- Change passwords and enable authenticator-based 2FA on all exchange accounts immediately
- Notify your bank if any fiat currency was transferred as part of the scam
- File reports with relevant authorities — detailed in the next section
Do not engage further with the scammer under any circumstances, even if they offer to return funds or propose a settlement. Every continued engagement is an opportunity for additional manipulation, and promises of restitution from active scammers are universally false. If the scam involved a romantic or emotional relationship, recognize that the person you developed feelings for was a constructed persona — that is a difficult reality, but accepting it is necessary to prevent further financial harm.
Where to Report Crypto Fraud in the US, UK, and Australia
Reporting a crypto scam will rarely result in immediate fund recovery, but it is not pointless. Law enforcement agencies use these reports to identify patterns, build cases against organized crime networks, and issue public warnings that protect future victims. In jurisdictions where crypto enforcement has improved — notably in the US and UK — reports have contributed to successful prosecutions and, in some cases, partial asset recovery through international law enforcement cooperation.
Where to Report Crypto Scams — By Jurisdiction
- 🇺🇸 USFBI IC3 at ic3.gov — FTC at reportfraud.ftc.gov — CFTC at cftc.gov/complaint
- 🇬🇧 UKAction Fraud at actionfraud.police.uk — FCA at fca.org.uk/consumers/report-scam
- 🇦🇺 AustraliaScamwatch at scamwatch.gov.au — ASIC at asic.gov.au/report-misconduct
- 🇪🇺 EUYour national financial regulator — Europol cybercrime at europol.europa.eu
- AllReport scam wallet addresses to Chainalysis, CipherTrace, or major exchanges — flagged addresses can be frozen if funds are routed through regulated platforms
Only About 10% of Stolen Crypto Is Ever Recovered — Stay Ahead of Scammers
That 10% recovery figure from the Chainalysis 2025 report is the most important statistic in this entire guide. It means that for every $10 stolen by crypto scams, $9 is gone permanently — no chargeback, no FDIC insurance, no customer service department that can reverse the transaction. The blockchain’s irreversibility, which makes it powerful, is also what makes crypto theft so final. Every tool, red flag, verification step, and wallet protection strategy in this guide exists for one reason: prevention is the only form of recovery that reliably works. Scammers are sophisticated, well-resourced, and constantly evolving their tactics — but they depend entirely on finding investors who haven’t done the work to recognize them. You’ve now done that work.
Frequently Asked Questions
Crypto scam tactics evolve constantly, but the underlying patterns — guaranteed returns, identity manipulation, urgency engineering, and platform fakery — remain consistent across nearly every type. The questions below address the most common points of confusion investors face when evaluating a platform or responding to an approach.
Many of the most effective scam defenses are not technical — they are behavioral. A personal rule that no investment recommendation from an online-only contact will ever be acted upon without 48 hours of independent research eliminates the majority of scam opportunities before they develop.
If you are currently questioning whether something you are involved with is a scam, the fact that you are questioning it is itself meaningful data. Legitimate investments do not typically leave investors feeling uncertain about the platform’s authenticity — that discomfort exists for a reason, and it is worth listening to before any further funds are committed.
How Can I Tell if a Crypto Investment Opportunity Is a Scam?
A crypto investment opportunity is likely a scam if it promises guaranteed returns, was introduced by someone you only know online, requires you to send crypto to receive more crypto, or operates on a platform you cannot verify through independent regulatory databases. Legitimate opportunities can withstand scrutiny — run the team through LinkedIn, check the contract on Etherscan, verify the domain age with WHOIS, and confirm regulatory registration with the relevant authority. If any of these checks fail or the opportunity cannot wait for you to complete them, walk away. For more on evaluating platforms, explore the best crypto research platforms available.
What Should I Do if Someone Asks for My Seed Phrase?
Refuse immediately and permanently. There is no legitimate scenario — technical support, wallet recovery, account verification, or any other reason — in which a real person, platform, or application needs your seed phrase. Your seed phrase is the complete, irrevocable key to your entire wallet. Anyone asking for it is attempting to steal everything in it. End the conversation, do not provide any partial information, and if you have any concern that your seed phrase may have been exposed, transfer your assets to a new wallet with a new seed phrase immediately.
Are Crypto Recovery Services Legitimate?
The overwhelming majority of crypto recovery services that approach victims — through Google ads, forums, social media, or direct outreach — are scams specifically targeting people who have already been victimized. This practice, sometimes called “recovery scamming,” has cost victims an additional $100,000 or more in documented cases according to the Chainalysis 2025 report.
There are a small number of legitimate blockchain forensics firms — Chainalysis, CipherTrace, and Elliptic among them — but these firms work primarily with law enforcement and financial institutions, not with individual retail victims seeking private recovery. They do not cold-contact victims through social media.
- ◆Any recovery service that contacts you unsolicited is almost certainly a scam
- ◆Legitimate forensics firms do not guarantee recovery or charge upfront fees to individuals
- ◆Recovery success rates from confirmed theft to an unknown scammer wallet are extremely low
- ◆Your best recovery channel is law enforcement reporting, not private services
If you are determined to pursue recovery, consult a licensed attorney with demonstrated blockchain litigation experience before engaging any private service. Legal professionals can assess the realistic options in your specific jurisdiction and will not demand upfront crypto payments to begin their work.
How Do I Report a Crypto Scam?
Report to as many relevant channels as possible — each report contributes to the intelligence picture that law enforcement and regulators use to identify and prosecute scam operations.
- IC3:ic3.gov — primary US federal reporting channel
- FTC:reportfraud.ftc.gov — for US consumers
- Action Fraud:actionfraud.police.uk — for UK victims
- Scamwatch:scamwatch.gov.au — for Australian victims
- Exchanges:Report scam wallet addresses to Binance, Coinbase, Kraken — flagged addresses can be frozen if funds route through regulated platforms
Do not pay anyone who offers to expedite your report or claims to have law enforcement connections that can accelerate recovery. Official reporting channels are free, and any person charging a fee to file a report on your behalf is running yet another scam targeting crypto fraud victims.
Can Stolen Crypto Ever Be Recovered?
In a small percentage of cases, yes — but the conditions required are specific and largely outside an individual victim’s control. Recovery is most likely when the scammer routes stolen funds through a regulated exchange that responds to law enforcement subpoenas, when a large-scale law enforcement operation dismantles an organized scam network, or when a DeFi protocol exploit involves an identifiable attacker who can be pressured through public exposure or legal action.
The Chainalysis 2025 report established that approximately 10% of stolen cryptocurrency finds its way back to victims — and that figure includes institutional recoveries from exchange hacks, which are more recoverable than individual scam losses. For individual pig butchering or romance scam victims, recovery rates are substantially lower.
The blockchain’s transparency works in your favor in one specific way: stolen funds can be tracked in real time as they move through wallets and exchanges. Services like Chainalysis Reactor, used by law enforcement globally, can follow the money trail even through multiple hops and mixing attempts. The most accurate framing is this: treat crypto as unrecoverable once stolen, invest heavily in prevention, and view any recovery that does occur as a fortunate exception rather than an expectation. Every verification step and red flag you catch is worth exponentially more than any recovery process after the fact.
Disclaimer
This article is for informational and educational purposes only. Do Your Own Research (DYOR) before making any cryptocurrency investment or engaging with any platform. The statistics cited are sourced from publicly available reports including Chainalysis and FBI IC3 publications. CoinPosters is not responsible for any financial losses arising from actions taken based on the information provided in this article. Always consult qualified legal or financial professionals regarding specific situations involving fraud or financial loss.
CoinPosters
Your guide to navigating crypto in 2026 and beyond.
Latest
Markets
25 Feb 2026
Markets
21 Feb 2026