Coinposters
Can Bitcoin Blockchain Be Hacked?

Because the Bitcoin blockchain is regularly examined by the whole network, Bitcoin is deemed hack-proof. Therefore, assaults on the blockchain itself are improbable.
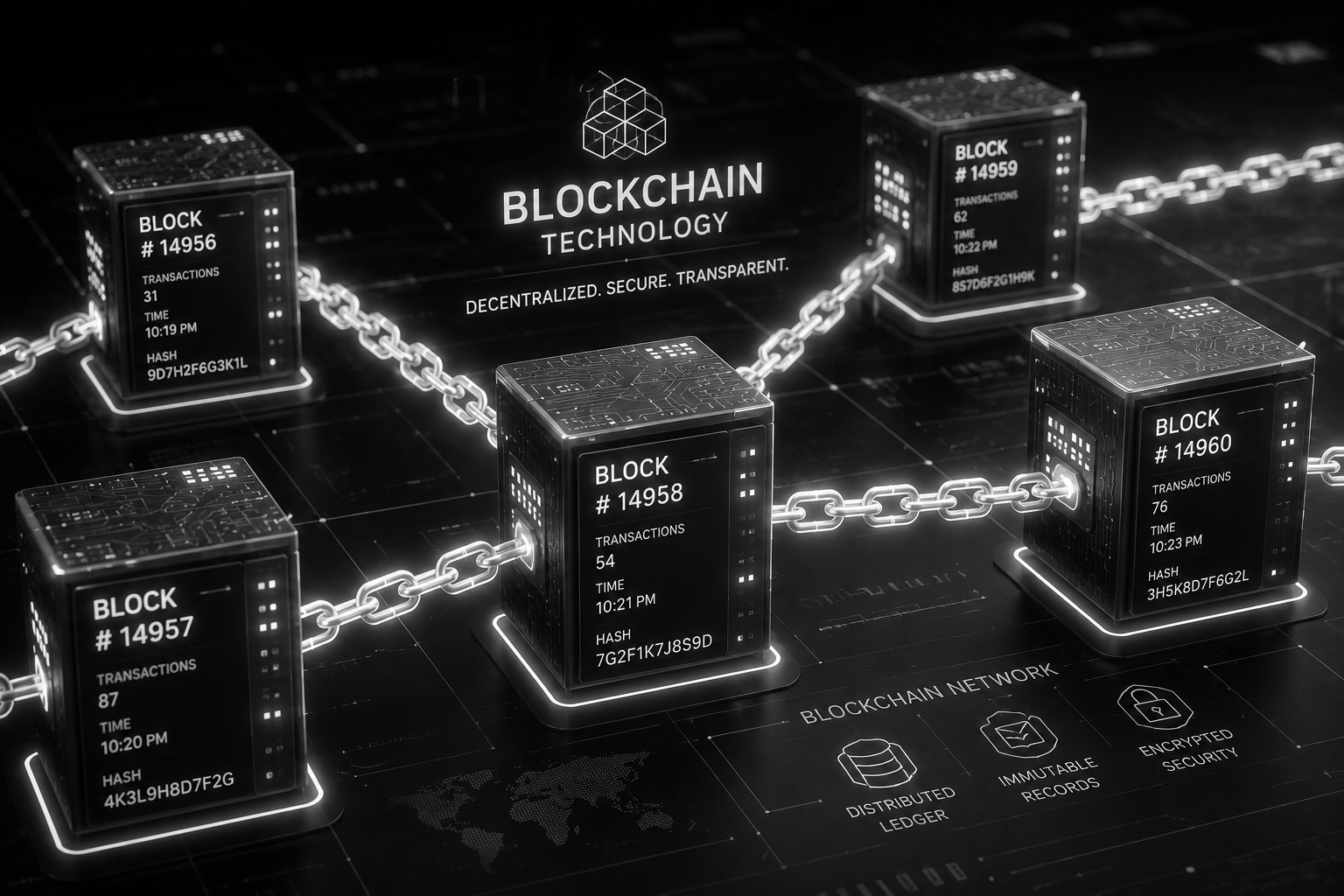
Bitcoin (BTC) combines both a blockchain database and a network of computers known as nodes that connect with one another to construct and update the database. The network contains hundreds of thousands of computers owned by a diverse group of individuals. Anyone with no qualifications may join this network.
This open system’s database has never been compromised. This is because compromising one computer’s database is inadequate to damage the databases of all other computers.
In fact, the other computers on the network will instantly notify the compromised user that their database has been damaged and will either assist them in correcting the issue or disconnect them from the network.
Even more striking is the fact that a single legitimate blockchain computer may fix an endless number of faulty or out-of-date chains. The network follows the objectively most valid chain rather than the majority’s view.
Just How Secure is Bitcoin Blockchain?
A blockchain’s security is handled using cryptographic algorithms and consensus processes. Blockchains encrypt transaction information and incorporate data from prior blocks in each subsequent block. Through encrypted data, the whole ledger is linked together. Each freshly formed brick strengthens it.
An attacker—or group of attackers—could gain control of a blockchain by controlling a majority of its processing power, known as hashrate. They may introduce a changed blockchain if they control more than 50% of the hashrate, which is known as a 51% assault.
This enables them to make modifications to transactions that were not validated by the blockchain prior to their takeover. When six confirmations have been received, a transaction is declared successful.
For example, if you sent 1 BTC to a buddy, the transaction would be recorded and validated in a single block—the first confirmation. This is the second confirmation.
The data from that block is recorded into the following block, verified, and the block is closed. This must be repeated four times more for the network to complete the transaction. In a 51% attack, transactions that have not been processed can be reversed.
Latest
Bitcoin
25 Feb 2026
Bitcoin
21 Feb 2026